Python Code Tutorials
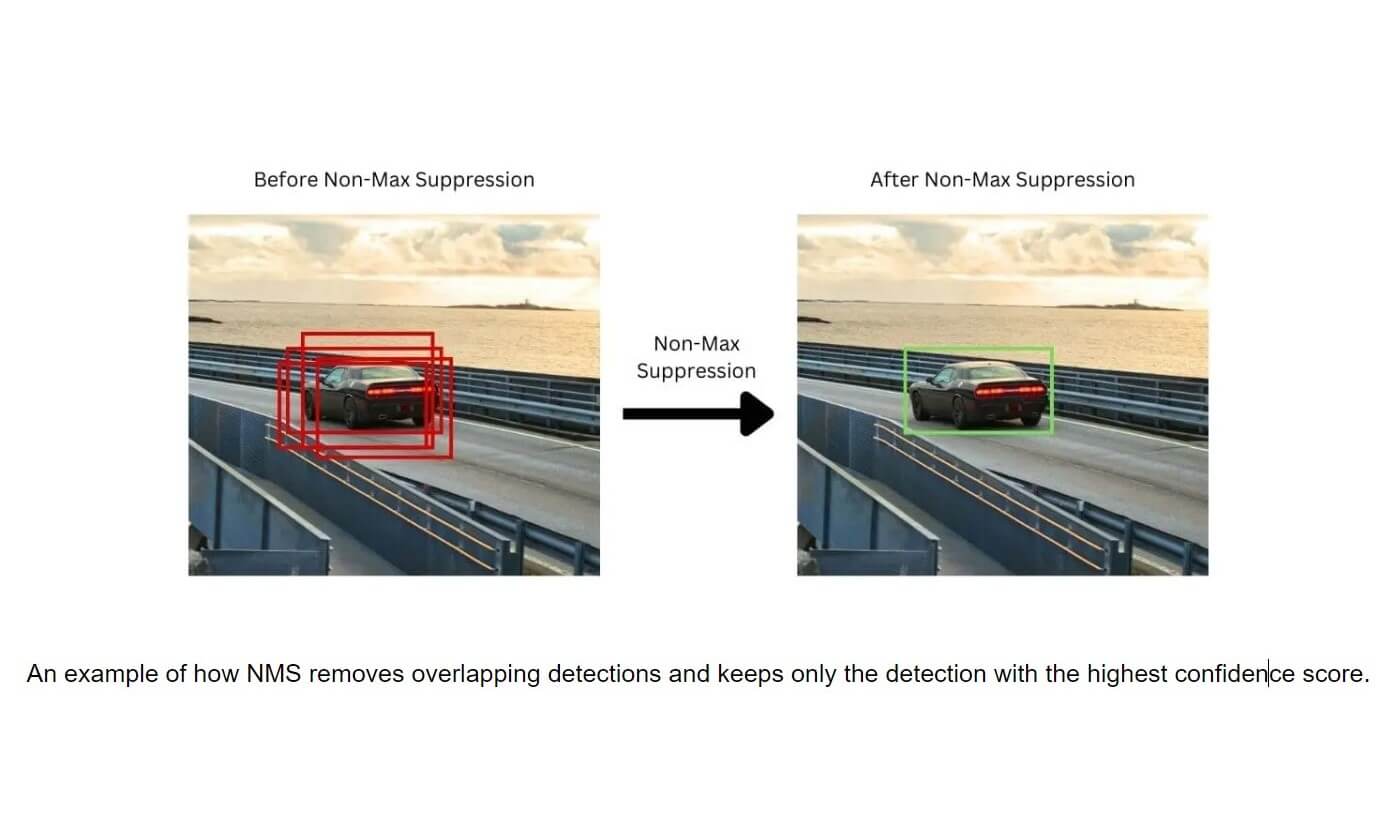
Non-Maximum Suppression with OpenCV and Python
Explore the critical role of Non-Maximum Suppression (NMS) in object detection to eliminate redundant bounding boxes, ensuring precise results. This guide covers NMS's workings, the importance of Intersection-over-Union (IoU), and how to implement NMS with OpenCV in Python.

How to Find Past Wi-Fi Connections on Windows in Python
Discover how to reveal all previously connected Wi-Fi networks on a Windows computer using Python, a crucial tool in digital forensics to unearth networks thought to be forgotten but stored in the Windows Registry.

How to Build Spyware in Python
Create a spyware in Python in this guide. Learn to build a surveillance tool that captures live video streams via a client-server architecture, with practical insights into network communication and video handling using OpenCV.
Why Learn Python for Data Science in 2024
Explore why you should learn Python programming language for learning data science in 2023

Why Python Is Used for Cybersecurity
This article delves into the importance of cybersecurity for online businesses and why Python is a go-to programming language for cybersecurity experts. It highlights Python's various benefits, such as its simplicity, extensive libraries, and versatility across platforms. The article also discusses Python's limitations

How to Remove Metadata from PDFs in Python
Learn to safeguard privacy by removing metadata from PDFs using Python's PyPDF2 in this tutorial. Discover how metadata can expose sensitive information and how to erase it to protect confidentiality, with step-by-step code guidance and practical examples.
Setting up Python on Mac: Installation Instructions and Running Your First Script
This article guides new MacBook users on setting up Python, checking for existing Python versions, and installing it if necessary. It also provides a step-by-step guide to running your first Python script.
Big Data Modeling in ClickHouse and PostgreSQL
This article compares ClickHouse and PostgreSQL for big data modeling, examining their approaches, advantages, and disadvantages. It aims to guide businesses in choosing the right database system for effectively managing and leveraging big data.
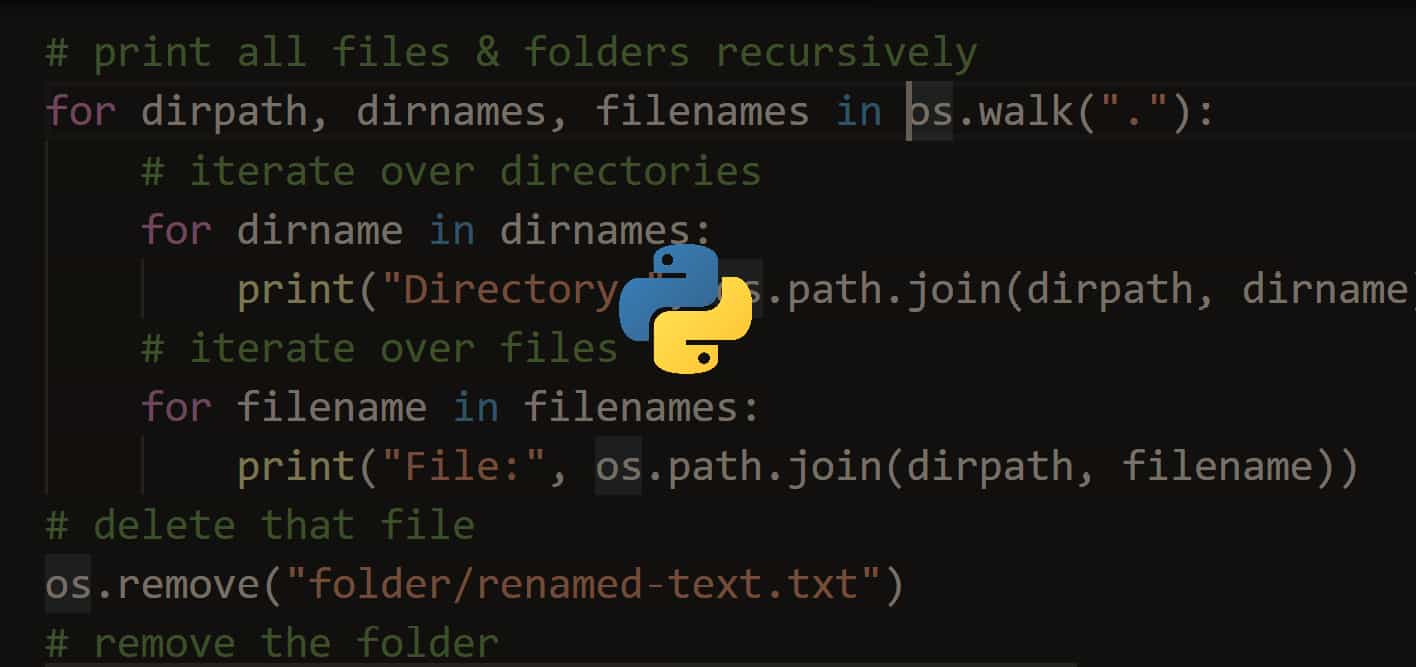
How to Make a Grep Clone in Python
Learn to build your own Python-based grep tool in this concise guide, perfect for bug hunting and pen-testing. Master text pattern searches within files and streams, saving time and effort in your development tasks.

How to Exploit Command Injection Vulnerabilities in Python
Automate the detection and exploitation of OS command injection vulnerabilities using Python. This comprehensive guide covers setting up a test environment with DVWA and Metasploitable, detecting vulnerabilities, and automating tests with custom scripts.

How to Make a Pacman Game with Python
Learn how to create a Pacman game using Python and Pygame with this comprehensive tutorial. Covering everything from setting up your environment, creating game characters and components, to running the game, this guide provides step-by-step instructions to build a fully functional Pacman game.

How to Make Malware Persistent in Python
Learn how to achieve persistence for malware using Python, ensuring it remains active after system reboots. This tutorial guides you through implementing persistence techniques on both Windows and Linux systems, from modifying registry settings to setting up cron jobs.

How to Remove Persistent Malware in Python
Learn how to detect and remove persistent malware using Python in this step-by-step tutorial. Explore methods for automating malware removal across Windows and Linux systems by manipulating startup entries and crontab files.