Unlock the secrets of your code with our AI-powered Code Explainer. Take a look!
Say you're tasked to investigate a suspect's computer, and you find a zip file that seems very useful but is protected by a password. In this tutorial, you will write a simple Python script that tries to crack a zip file's password using dictionary attack.
Note that there are more convenient tools to crack zip files in Linux, such as John the Ripper or fcrackzip. The goal of this tutorial is to do the exact same thing but with Python programming language.
Get: Build 35+ Ethical Hacking Scripts & Tools with Python EBook
We will be using Python's built-in zipfile module, and the third-party tqdm library for quickly printing progress bars:
pip3 install tqdmAs mentioned earlier, we gonna use dictionary attack, which means we will need a wordlist to brute force this password-protected zip file. For this tutorial, we will use the big rockyou wordlist (with a size of about 133MB). If you're on Kali Linux, you can find it under the /usr/share/wordlists/rockyou.txt.gz path. Otherwise, you can download it here.
You can also use the crunch tool to generate your custom wordlist as you exactly specify.
Related: How to Crack PDF Files in Python.
Open up a new Python file and follow along:
import zipfile
from tqdm import tqdmLet's specify our target zip file along with the word list path:
# the password list path you want to use, must be available in the current directory
wordlist = "rockyou.txt"
# the zip file you want to crack its password
zip_file = "secret.zip"To read the zip file in Python, we use the zipfile.ZipFile class that has methods to open, read, write, close, list and extract zip files (we will only use extractall() method here):
# initialize the Zip File object
zip_file = zipfile.ZipFile(zip_file)
# count the number of words in this wordlist
n_words = len(list(open(wordlist, "rb")))
# print the total number of passwords
print("Total passwords to test:", n_words)Notice we read the entire wordlist and then get only the number of passwords to test. This can prove useful for tqdm so we can track where we are in the brute-forcing process. Here is the rest of the code:
with open(wordlist, "rb") as wordlist:
for word in tqdm(wordlist, total=n_words, unit="word"):
try:
zip_file.extractall(pwd=word.strip())
except:
continue
else:
print("[+] Password found:", word.decode().strip())
exit(0)
print("[!] Password not found, try other wordlist.")Related: Build 35+ Ethical Hacking Scripts & Tools with Python EBook
Since wordlist now is a Python generator, using tqdm won't give much progress information. That's why I introduced the total parameter to give tqdm insight into how many words are in the file.
We open the wordlist and read it word by word, and try it as a password to extract the zip file; reading the entire line will come with the new line character. As a result, we use the strip() method to remove white spaces.
The method extractall() will raise an exception whenever the password is incorrect, so we can proceed to the next password, in that case. Otherwise, we print the correct password and exit the program.
I have edited the code a little to accept the zip and wordlist files from command line arguments. Check it here.
Check my result:
root@rockikz:~# gunzip /usr/share/wordlists/rockyou.txt.gz
root@rockikz:~# python3 zip_cracker.py secret.zip /usr/share/wordlists/rockyou.txt
Total passwords to test: 14344395
3%|▉ | 435977/14344395 [01:15<40:55, 5665.23word/s]
[+] Password found: abcdef12345DISCLAIMER: Use this script to a file you have permission to access. Otherwise, we are not responsible for any misuse.
As you can see, I found the password after around 435K trials, which took about a minute on my machine. Note the rockyou wordlist has more than 14 million words which are the most frequently used passwords sorted by frequency.
Alright, we have successfully built a simple but useful script that cracks the zip file password. Try to use much more bigger wordlists if you failed to crack it using this list.
If you want to build a strong password, then make sure you use a password generator.
I highly encourage you to use multiple threads to crack the password much faster. If you succeed in doing so, please share your results with us in the comments below!
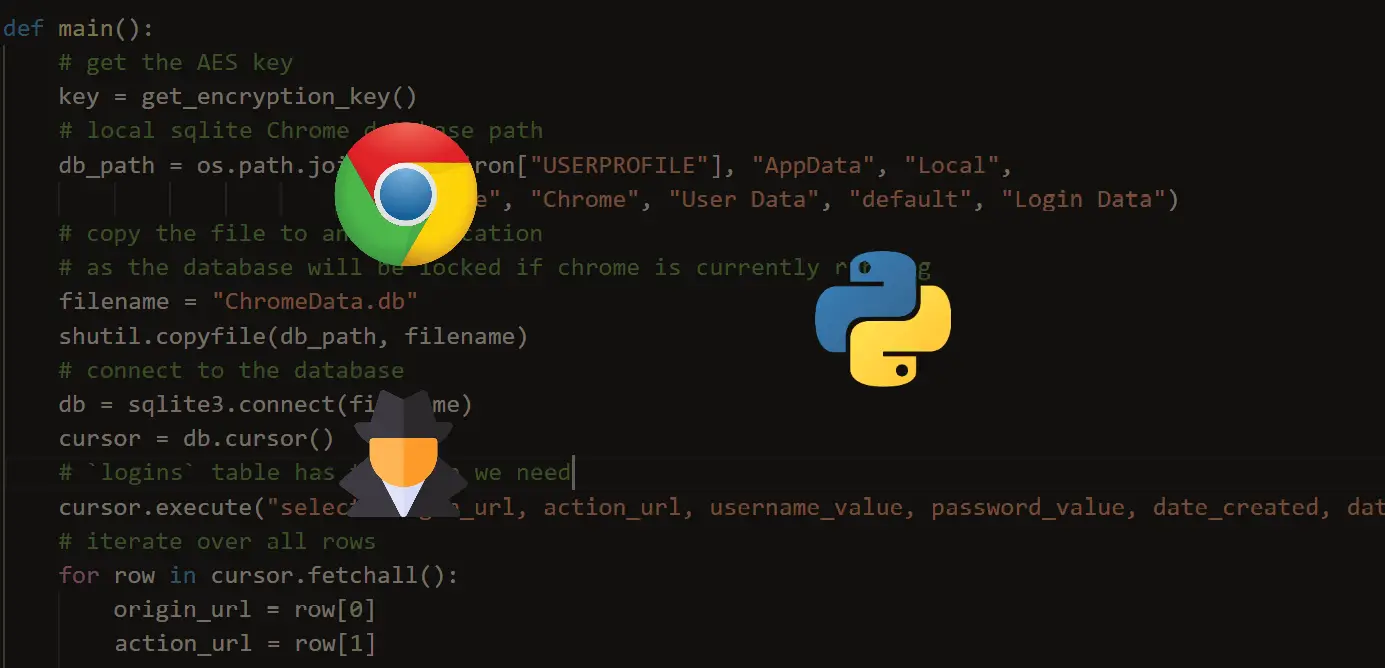
Finally, in our Ethical Hacking with Python EBook, we have built various password crackers, including this ZIP file cracker. You can check it here for more details; we built over 35 hacking tools and scripts from scratch using Python!
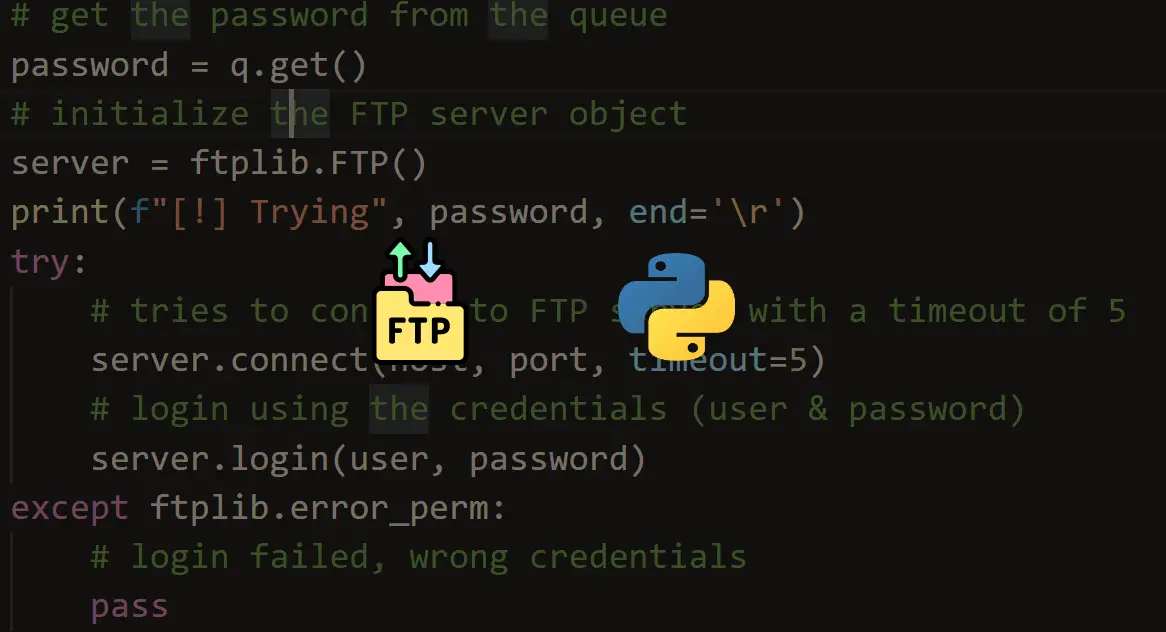
Read also: How to Brute Force FTP Servers in Python.
Happy Cracking ♥
Liked what you read? You'll love what you can learn from our AI-powered Code Explainer. Check it out!
View Full Code Explain My Code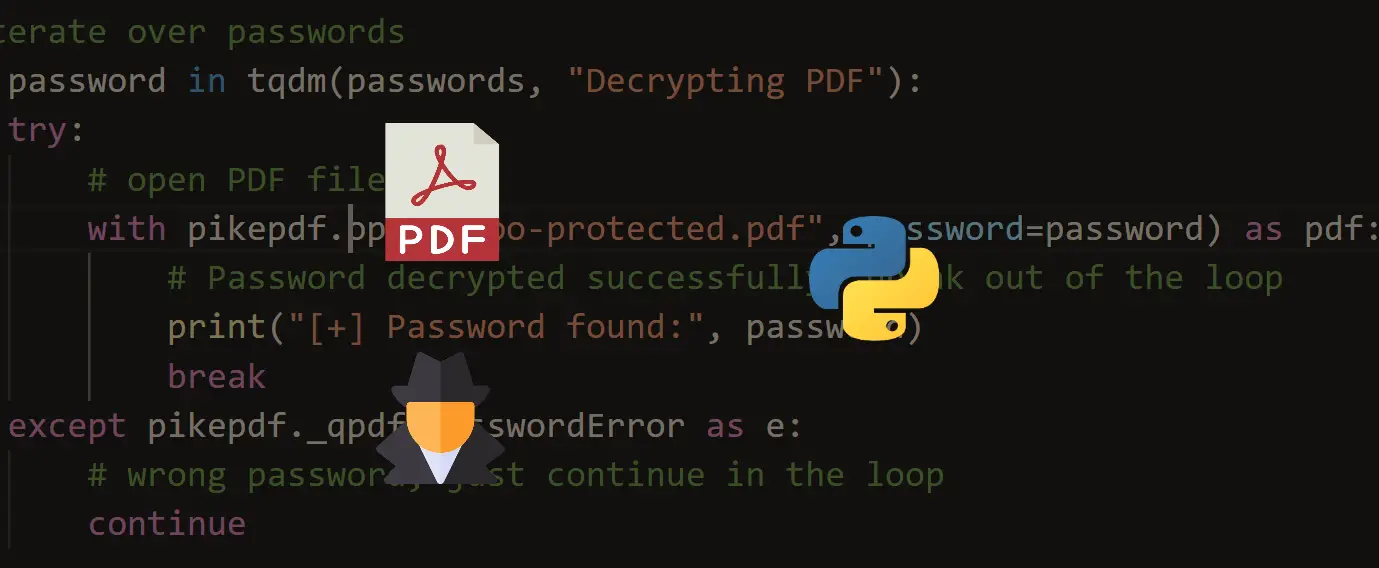

Got a coding query or need some guidance before you comment? Check out this Python Code Assistant for expert advice and handy tips. It's like having a coding tutor right in your fingertips!